Table of Contents
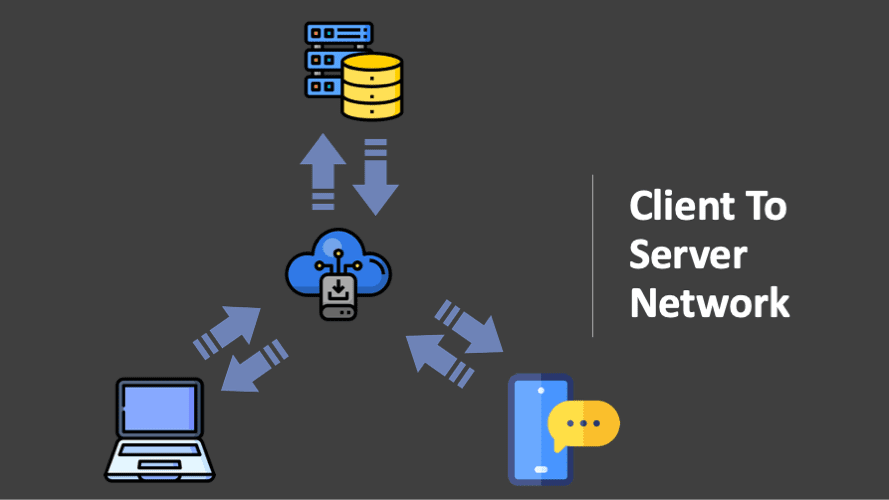
ToggleClient to server network or architecture is a computer approach in which the server hosts, distributes and controls most of the resources and services to be consumed by the client. This sort of architecture has one or more client computers connected to a central server through a network or internet connection. Client to server network is also known as a networking computer paradigm since all the requests and services are given through a network.
Components of Client to Server Network
- Client: Clients, also known as service requesters, these are pieces of computer hardware or server software that request resources and services made accessible by a server.
- Server: A server is a device or computer program that offers functionality for other devices or applications. Any computerized operation that may be used or called upon by a client to share resources and distribute tasks is a server. For eg : Application Server, Web Server etc.
- Network Devices: Network devices connect client to servers. They guarantee client to server communication and ensures that messages/requests are routed appropriately to the relevant server. There are several network devices and each give distinct forms of network access.
In a basic client to server network, a hub can link a server to numerous clients. It serves as a repeater, passing on data from one device to another.
Fat or Thin Client/Server
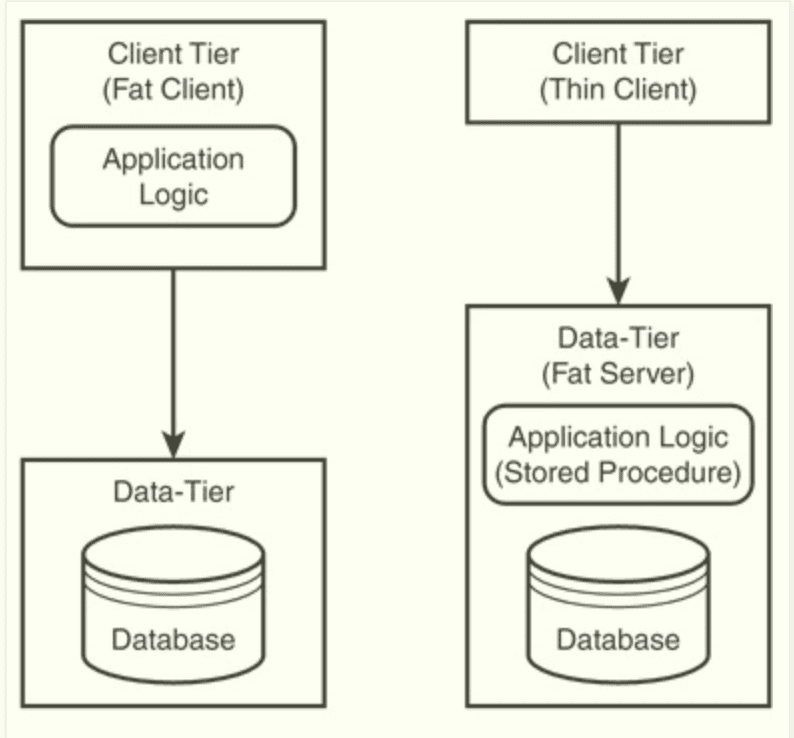
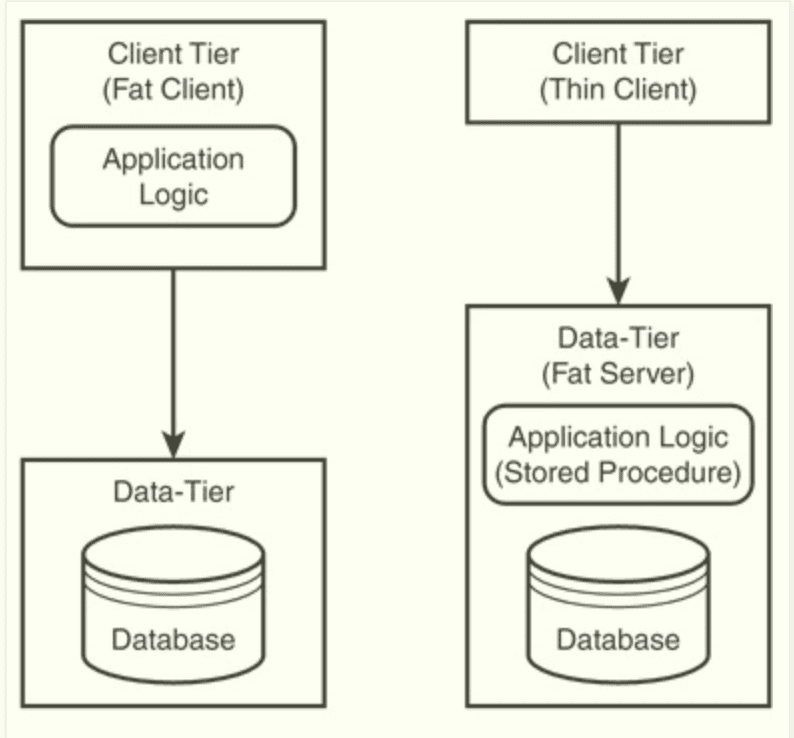
A Client or a Server is so termed based on the extent to which the processing is divided between the client and server.The notion of Fat Clients or Fat Servers is supplied by one of the main requirements, that is, how much of an application is located at the client end vs. the server end.
Fat Clients: This design provides additional application functionality on the client machine.
They are utilized in conventional of client to server network. Their use might be a maintenance burden for client to server architecture.
Fat Servers: This design places additional application functionality on the server machine. Typically, the server delivers more abstract, higher level services.
The current tendency is increasingly towards fat servers in client to server network. In that situation, the client is frequently detected utilizing a fast web browser.
The main advantage of utilizing the fat server is that it is easier to administer because just the software on the servers has to be upgraded, thereby reducing the pain of upgrading possibly hundreds of client computers.
Types of Client to Server Architecture
There are three main categories of client to server network
Two-tier Client to server network :
The design of every client to server architecture is by definition at least a two-tier system, the client being the first tier and the server being the second. The Client requests services directly from server i.e. client communicates directly with the server without the help of another server or server process.
In a typical two-tier system, SQL queries are issued by the application and then sent on by the driver to the database for execution.
The findings are then transmitted back using the same process, but in the reverse manner. It is the duty of the driver (ODBC) to provide the SQL query to the database in a manner that the database understands.
Advantages:
1. Architecture maintains a permanent connection between the client and database, therefore avoiding cost associated with the opening and closure of connections.
2. Faster than three-tier implementation.
3. It offers a great degree of flexibility and ease in management.
4. The application with two-tier architecture can be built in a comparably short period.
Disadvantages:
1. As the application development is done on client side, maintenance cost of application and client side tools etc. is high. That is why in two-tier architecture the client is termed ‘fat client’.
2. Since real processing of data happens on the remote client, the data has to be transmitted across the network. This leads to the increased network stress.
3. Applications are loaded on individual PC i.e. each application is bound to an individual PC. For this reason, the application logic cannot be reused.
Three-tier Client to server network:
In three-tier network, a third server is utilized to process requests from the client and then pass them off to the database server. The third server acts as proxy for all client requests
All client queries for the database are directed through the proxy server, therefore establishing a more secure environment for your database.
In two-tier context, we may say that the client utilizes a driver to transform the client’s request into a database native library call. In a three-tier system, the driver converts the request into a “network” protocol and then makes a request via the proxy server.
The proxy server makes the database request on behalf of the client and delivers the results back once they have been handled by the database. This method avoids the requirement for DBMS to be located on the same server.
Advantages:
- Load balancing is easier with the separation of the main business logic from the database server.
- Change management is easier and faster to accomplish. This is because a business logic is implemented on the server rather than providing many PCs with new program versions.
- Clear separation of user-interface-control and data display from application logic. Through this separation more clients are able to have access to a wide selection of server applications.
Disadvantages:
- The client does not maintain a permanent database connection.
- A second proxy server may be necessary.
- The network protocol utilized by the driver may be proprietary.
- Higher network traffic can be observed if a different proxy server is utilised.
N-tier Client to server network:
N-Tier architecture is also known as a “Multitier Design”, thus its scaled variant of the 3-tier client to server architecture. The GUI logic, app processing, and even data management functions are segregated from one another in this design.
N-tier architecture obliges developer to design components according to a business schema that represents entities, relationship, activities roles, and rules, thereby enabling them to distribute functionality across logical and physical tiers, allowing better utilization of hardware and platform resources, as well as sharing of those resources and the components that they support to serve several large applications at the same time.
Advantages:
- Overall performance has been enhanced as traffic is distributed to various servers.
- The business logic is centralized. Thus maintance and updation to business logic is very easy.
- Enhanced security level is reached as all the micro functions are segregated from one another, thus if one server goes down or comes in attack of hackers, the whole system is not compromised.
Disadvantages:
- Clients are still prone to viruses, worms, and Trojans if present in a Server or uploaded in the Server.
- Data packets can be modified or spoofed during the transmission.
Final Words
One of the main difficulties with a typical client to server network is the nature of unexpected workloads.In defining client to server architecture as systems that grow vertically and employ central data storage, some experts feel that peer-to-peer is more adaptable and versatile for making sure that unpredictable workloads are managed properly.
With the advent of decentralized and distributed systems, for example, blockchain technology, peer-to-peer networks are becoming more widespread and starting to replace client/server designs.